Access Management Extensions
Keycloak Advanced Authentication
We offer the Keycloak Advanced Extension Pack (SPIs) to enhance both the user experience and functionality of Keycloak.
Get Started
Keycloak Advanced Authentication
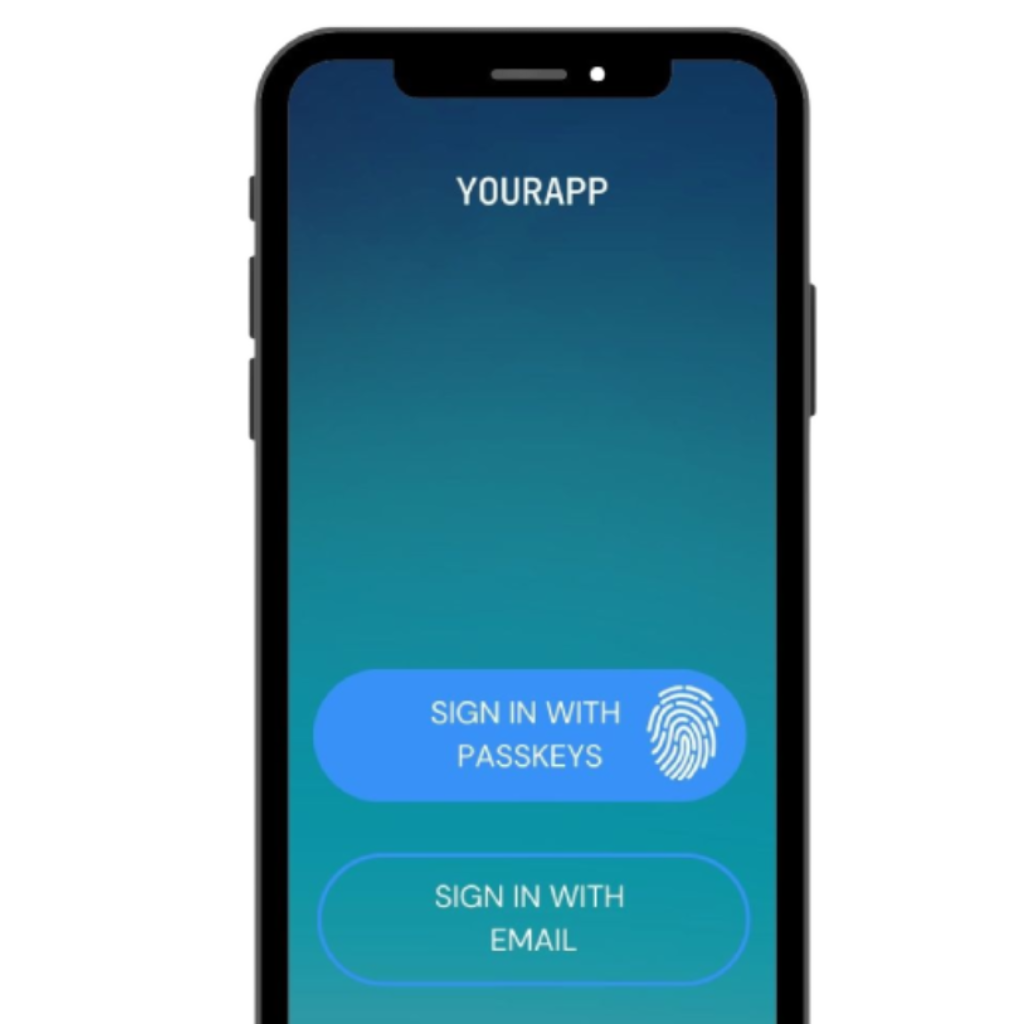
We introduce a native authentication experience in Keycloak through an API-based approach. With this method, the application controls each authentication step based on structured flow metadata returned by the Identity Provider, with no browser redirect required.
In parallel, we provide advanced authentication mechanisms that extend Keycloak's built-in capabilities for both browser and native application experiences.
Native Authentication
API-Based Authentication: Application Controls the Journey
Our native authentication approach is based on the proposed OAuth 2.0 standard for First-Party Apps (FiPA). Instead of redirecting users to the Identity Provider, the application drives each step natively based on structured flow metadata returned by the IdP. Any authenticator configured in the IdP (passkeys, OTP, biometric) is handled inside the application without a browser context switch.
Advanced Authentication Pack
Supported Authentication Mechanisms
Each mechanism is implemented as a Keycloak SPI and available in both browser and native application flows. The native column indicates support for API-based authentication via OAuth 2.0 FiPA, where the application controls the login experience directly.
Device-bound, phishing-resistant authentication based on the FIDO2/WebAuthn standard. Supports platform authenticators (Touch ID, Face ID, Windows Hello) and roaming authenticators (FIDO2 security keys).
One-time password delivered via SMS. Simple, widely supported, and compatible with any mobile device. Works for both primary login and step-up authentication scenarios.
One-time password delivered via email. No external SMS provider required. Ideal for users without reliable mobile access and for low-friction passwordless login flows.
Authenticate on a secondary device using the OAuth 2.0 Device Authorization Grant. Ideal for smart TVs, CLI tools, and limited-input devices where entering credentials directly is impractical.
Deploy the extensions in just a few easy steps.
The Keycloak extensions are a library that includes several Service Provider Interfaces (SPIs) to enhance Keycloak's functionality.
Step 1: Download
Get an active subscription and download the extensions from our private GitHub repository.
Step 2: Add the extensions
Deploy the extension JAR into your Keycloak installation.
Step 3: Configure your journey
Create your authentication flow based on your requirements: browser, native, or both.
Ready!
Keycloak Advanced Authentication
We are continually evolving our advanced authentication features to keep pace with the latest identity standards. Our company philosophy is to adhere to these standards, as they ensure both security and interoperability.